Cyber threats are becoming increasingly sophisticated, making it more important than ever to protect your network and data. Network security assessments can help you identify and address potential vulnerabilities, ensuring that your network remains secure.
This blog post will explore the world of network security assessments, covering everything from the different types of assessments to the benefits of conducting them. We will also provide tips on how to choose a network security assessment vendor, prepare for an assessment, and remediate findings.
What is network security assessment?
A network security assessment is a comprehensive evaluation of your network’s security posture. It involves identifying and assessing vulnerabilities, weaknesses, and potential threats. The goal of a network security assessment is to identify and remediate any security risks before they can be exploited by attackers.
Different types of network security assessments
There are two main types of network security assessments: vulnerability assessments and penetration testing.
- Vulnerability assessments use automated tools to scan your network for known vulnerabilities. This type of assessment can help you identify which vulnerabilities are present on your network and prioritize remediation efforts.
- Penetration testing simulates real-world attacks to identify and exploit vulnerabilities in your network. This type of assessment can help you understand how your network would withstand a real-world attack and identify any security weaknesses that need to be addressed.
Benefits of conducting a network security assessment
There are many benefits to conducting a network security assessment, including:
- Identifying and remediating security vulnerabilities: Network security assessments can help you identify and remediate security vulnerabilities before they can be exploited by attackers.
- Improving your security posture: By addressing the findings of a network security assessment, you can improve your overall security posture and make your network less vulnerable to attack.
- Meeting compliance requirements: Many industries have compliance requirements that require businesses to conduct regular network security assessments.
How often should I conduct a network security assessment?
The frequency of network security assessments depends on a number of factors, including the size and complexity of your network, the industry you operate in, and your compliance requirements. However, it is generally recommended to conduct network security assessments at least once a year.
How do I choose a network security assessment vendor?
When choosing a network security assessment vendor, it is important to consider the following factors:
- Experience and expertise: Choose a vendor with experience and expertise in conducting network security assessments.
- Methodology: Make sure the vendor uses a comprehensive methodology that covers all aspects of network security.
- Tools and technologies: Ask the vendor about the tools and technologies they use to conduct network security assessments.
- Cost: Get quotes from multiple vendors before making a decision.
Importance of network security assessment
Network security assessments are essential for businesses of all sizes. By identifying and remediating security vulnerabilities, network security assessments can help businesses protect their data, systems, and reputation from cyber attacks.
Common network security vulnerabilities
Some of the most common network security vulnerabilities include:
- Misconfigured security devices
- Weak passwords
- Unpatched software
- Open ports and services
- Malicious code
Steps to conduct a network security assessment
The following steps are involved in conducting a network security assessment:
1. Plan the assessment: This involves defining the scope of the assessment, identifying the assets to be assessed, and developing a schedule.
2. Gather information: This involves collecting information about the network, such as its architecture, topology, and security controls.
3. Identify vulnerabilities: This involves using a variety of tools and techniques to identify vulnerabilities in the network.
4. Assess risks: This involves assessing the likelihood and impact of each vulnerability.
5. Prioritize remediation: This involves prioritizing the remediation of vulnerabilities based on their risk level.
6. Report findings: This involves generating a report that documents the findings of the assessment and provides recommendations for remediation.
Tools for network security assessment
There are a variety of tools available for conducting network security assessments. Some of the most popular tools include:
1. Nmap
2. Nessus
3. OpenVAS
4. Metasploit
5. Wireshark
Best practices for network security assessment
- Engage a qualified team: Network security assessments should be conducted by a qualified team with experience and expertise in the field.
- Use a comprehensive methodology: A comprehensive methodology should cover all aspects of network security, including vulnerability scanning, penetration testing, and risk assessment.
- Get buy-in from stakeholders: It is important to get buy-in from all stakeholders before conducting a network security assessment. This will help ensure that the assessment is conducted smoothly and that any findings are addressed promptly.
- Communicate findings effectively: The findings of the network security assessment should be communicated to stakeholders in a clear and concise manner. This will help ensure that everyone understands the risks and can take appropriate action.
Benefits of regular network security assessments
Regular network security assessments offer a number of benefits, including:
- Improved security posture: By regularly identifying and remediating security vulnerabilities, organizations can improve their overall security posture and make their networks less vulnerable to attack.
- Reduced risk of data breaches: Data breaches can have a devastating impact on organizations, both financially and reputationally. Regular network security assessments can help organizations reduce the risk of data breaches by identifying and addressing security vulnerabilities before they can be exploited by attackers.
- Compliance with regulations: Many industries have compliance requirements that require organizations to conduct regular network security assessments. By conducting regular assessments, organizations can ensure that they are meeting their compliance requirements.
Network security assessment checklist
The following checklist can be used to help ensure that your network security assessment is comprehensive:
- Vulnerability scanning: Has the network been scanned for known vulnerabilities?
- Penetration testing: Has the network been tested to simulate real-world attacks?
- Risk assessment: Have the risks associated with each vulnerability been assessed?
- Prioritized remediation: Have the vulnerabilities been prioritized for remediation?
- Reporting: Has a report been generated that documents the findings of the assessment and provides recommendations for remediation?
What are the best practices for preparing for a network security assessment?
The following are some best practices for preparing for a network security assessment:
- Gather documentation: Gather all relevant documentation for your network, including network diagrams, security policies, and system configurations.
- Identify assets: Identify all of the assets that need to be assessed, such as servers, workstations, and network devices.
- Develop a schedule: Develop a schedule for the assessment and communicate it to all stakeholders.
- Prepare for downtime: Some network security assessments may require some downtime for your network. Be sure to prepare for this downtime and communicate it to users in advance.
How do I remediate the findings of a network security assessment?
Once you have received the findings of your network security assessment, you should prioritize and remediate the vulnerabilities. The specific remediation steps will vary depending on the nature of the vulnerability. However, some common remediation steps include:
- Patching software
- Changing passwords
- Configuring security devices correctly
- Closing unnecessary ports and services
- Removing malware
How do I measure the success of a network security assessment?
The success of a network security assessment can be measured by the following factors:
- Number of vulnerabilities identified and remediated: The more vulnerabilities that are identified and remediated, the more successful the assessment will be.
- Reduction in risk: The assessment should reduce the overall risk to your network.
- Improved security posture: The assessment should improve your overall security posture and make your network less vulnerable to attack.
What are the latest trends in network security assessment?
Some of the latest trends in network security assessment include:
- Increased use of automation: Automation is being used to make network security assessments more efficient and effective.
- Focus on cloud security: Cloud security is becoming increasingly important as more businesses move to the cloud. Network security assessments are being adapted to assess cloud environments.
- Use of artificial intelligence (AI): AI is being used to develop new tools and techniques for network security assessments.
How can I automate network security assessments?
A number of tools are available to automate network security assessments. These tools can help you scan your network for vulnerabilities, assess risks, and prioritize remediation efforts. Some popular network security assessment automation tools include:
- Rapid7 Nexpose
- Qualys Vulnerability Management
- Tenable Nessus
- IBM Security QRadar
- Microsoft Defender for Cloud
How can I integrate network security assessments with my other security tools and processes?
Network security assessments can be integrated with other security tools and processes in a number of ways. For example, you can integrate the results of network security assessments into your security information and event management (SIEM) system. This will allow you to correlate security events from different sources and identify potential threats.
You can also integrate network security assessments into your vulnerability management process. This will help you prioritize remediation efforts and track your progress over time.
How can I use network security assessments to improve my security posture?
Network security assessments can be used to improve your security posture in a number of ways. By regularly identifying and remediating security vulnerabilities, you can make your network less vulnerable to attack.
You can also use network security assessments to assess the effectiveness of your security controls. This will help you identify any areas where your security posture needs to be improved.
How can I use network security assessments to comply with industry regulations?
Many industries have compliance requirements that require organizations to conduct regular network security assessments. By conducting regular assessments, you can ensure that you are meeting your compliance requirements.
Conclusion: Ensuring a secure network for your business
Network security assessments are an essential part of protecting your business from cyber threats. By regularly identifying and remediating security vulnerabilities, you can improve your overall security posture and make your network less vulnerable to attack.
If you do not have the in-house expertise to conduct network security assessments, you may want to consider hiring a network security professional. Network security professionals have the knowledge and experience to conduct comprehensive and effective network security assessments.
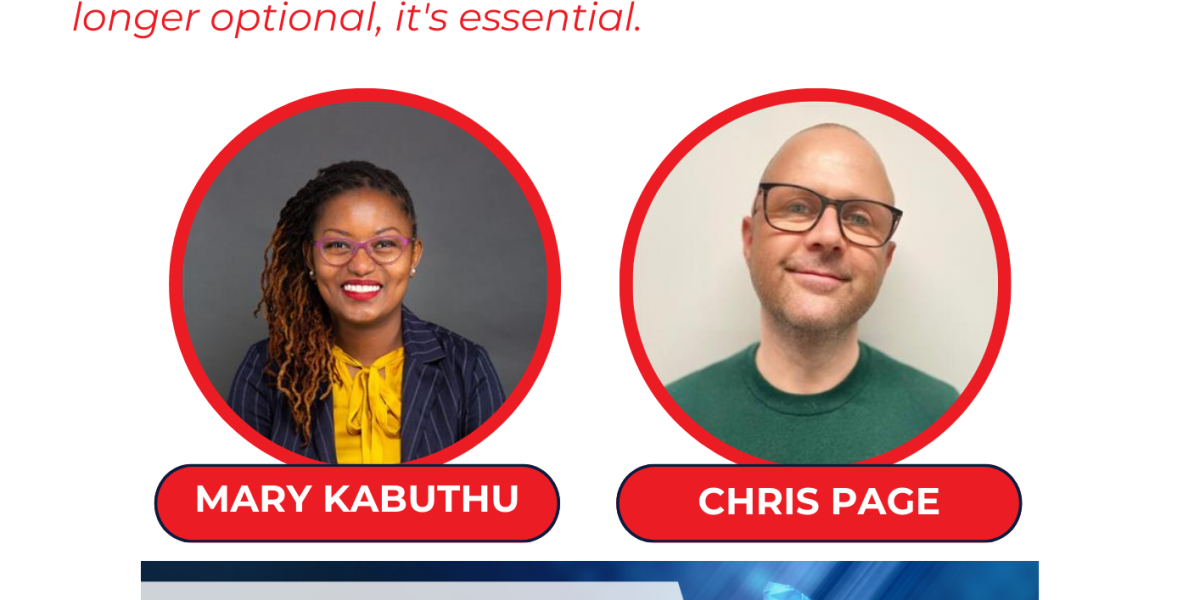
Yes, Treten Networks in partnership with Netscout is a preferred network security assessment provider. Treten Networks is a Cisco Gold Partner and Netscout is a leading provider of network security solutions. The partnership between these two companies allows Treten Networks to offer its customers comprehensive and effective network security assessments using Netscout’s cutting-edge security solutions.
Feel free to explore https://www.tretennetworks.com/get-a-quote and secure your FREE CONSULTATION.